Normally when you need to secure your important data from other users, then your first choice is to burn it on CD or put it to removable drive instead of hard drive. But imagine if your data size is more than 100 GB then it is not easy to burn it on CD. No worry, you can save your full drive from other users access using this trick. Check out InfoSec Institute for IT courses including computer forensics boot camp training
Perform the given steps to hide your system data partition:
-
To enable this feature, you will need to be logged into your computer with administrative rights.
-
-
First click on Start button to open "Run" and type "CMD" (without the quotes) then press Ok button to open Command Prompt.

Now type diskpart on the blinking cursor and wait for 5 seconds to appear diskpart> utility.

To show the list of volume, type list volume command after the diskpart> prompt, this command will show you all system drives detail.

if you need to hide F drive then first type select volume 2 (in this case) and press enter button.

After loading volume, type remove letter F (in this case) to hide F drive.

Now exit from command prompt and open My Computer to verify drives.
But next time, when you want to unhide the D drive, just run assign drive F command after loading volume 2.



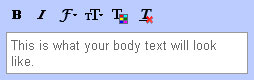
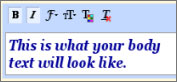 Now click on the Compose button and type in something; you will see the formatting by default. You can revert back to the default formatting style by clicking on the Remove Formatting button on the toolbar while creating a new email message.
Now click on the Compose button and type in something; you will see the formatting by default. You can revert back to the default formatting style by clicking on the Remove Formatting button on the toolbar while creating a new email message.












































