The biggest threats to IT security don’t originate from outside a company. Employees, contractors, and business partners on the inside pose a far greater security risk. As long as your current or former staff and associates have access to your internal network, you are vulnerable to a security breach.
Here’s how to deal with the real and significant threat of attack from insiders, and avoid the widespread damage they can unleash on your company’s finances and reputation.
First: Assess the Risk
For most firms, implementing full protection against every possible threat is not feasible. It makes more sense to assess the risk, determining which data is critical and which is relatively unimportant. Protect critical resources first.
Next, decide who needs access to the network. Make sure that individuals such as partners, suppliers and contractors have access only to the information they need to serve your company or customers.
The third step in assessing risk is determining who are the potential threats, why they would want access to the network, and how they could gain entry. At this stage, many organizations only consider external threats: competitors, random hackers or former employees. Don’t neglect analyzing your insider threats, as well – including the staffers tasked with protecting the system.
Next, decide who needs access to the network. Make sure that individuals such as partners, suppliers and contractors have access only to the information they need to serve your company or customers.
The third step in assessing risk is determining who are the potential threats, why they would want access to the network, and how they could gain entry. At this stage, many organizations only consider external threats: competitors, random hackers or former employees. Don’t neglect analyzing your insider threats, as well – including the staffers tasked with protecting the system.
Once you’ve uncovered vulnerabilities, you can take steps to prevent an insider attack.
Implement Preventative Measures
Among the best practices for preventing insider threats are:
- Institute clear policies and controls; be sure all employees are aware of acceptable network use and what constitutes a breach.
- Enforce policies consistently; maintain proper paper trails.
- Implement security awareness training; reinforce its importance.
- Segregate duties to reduce risk.
- Encourage employees to come forward and identify suspicious behavior, malicious insiders, threats against the company or attempts at exploitation.
- Implement proper system administration safeguards on critical servers.
- Monitor trusted users.
- Audit access to customer information.
Finally, Know Whom You’re Hiring
Failing to thoroughly check out a potential hire leaves a company vulnerable to insider threats. It goes without saying that thorough background checks are necessary for any prospective new employee who will have access to sensitive information, from customer credit card numbers to crucial application source codes. But for better protection, extend that practice to all employees and contractors.
Background checks should include a criminal history report, a credentials check and a credit check. Hiring managers should verify past employment and speak to former employers regarding the applicant’s history of dealing with workplace issues. Any information gathered should be part of the decision-making process.
Monitor Employee Behavior
Once an employee is hired, be sure supervisors are tasked with reporting any strange or inappropriate behavior. Compare such incidents to systems logs to determine if anything unusual is happening. And remember to enforce all security policies. If employees learn they can get away with small violations, they may be emboldened to move on to bigger and more lucrative security breaches.
Be Aware and Vigilant When Dealing With Insider Threats
Whether they modify data, steal critical codes, sell company secrets or commit payroll fraud, insiders are the biggest security threats a company will face. While there is always an element of risk, you can decrease information system vulnerability with these common sense steps. Most importantly, by being aware and vigilant, you’ll be better prepared to avoid the losses that far too many organizations suffer at the hands of trusted insiders.
As more companies move more of their businesses online we should expect to see more threats. Formal IT security training can help defend against these threats. Consider Villanova University’s online programs such as their CISSP certification prep courses
As more companies move more of their businesses online we should expect to see more threats. Formal IT security training can help defend against these threats. Consider Villanova University’s online programs such as their CISSP certification prep courses



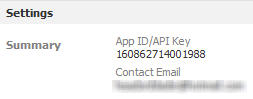 You can find your API key by opening the app settings from Facebook developers page. Replace the your-app-ID above with the app ID you just copied and follow the link. You will see options for adding the app or the canvas to your pages.
You can find your API key by opening the app settings from Facebook developers page. Replace the your-app-ID above with the app ID you just copied and follow the link. You will see options for adding the app or the canvas to your pages.